Đối tác uy tín XVIP
XVIP – Cổng Game Bài Đổi Thưởng 2025
Xvip đã thành công khi xây dựng được thương hiệu là cổng game uy tín và hiện đại nhất hiện nay. Cùng với kho game đồ sộ đã giúp người chơi được đắm chìm vào thế giới đặt cược trực tuyến đầy ấn tượng và kịch tính. Cổng game đã và đang nỗ lực để mang tới trải nghiệm trọn vẹn nhất dành cho người tham gia!
Tóm tắt
- Cổng game Xvip có giấy chứng nhận hợp pháp từ Isle Of Man Gambling Supervision Commission chứng minh được sự an toàn và uy tín.
- Cổng game sở hữu kho game đồ sộ như: game casino siêu hiện đại, game nổ hũ (slots) hấp dẫn, game bài đổi thưởng xanh chín.
- Hiện tại Xvip nhận được 300.000 lượt tải và hơn 1.000 lượt chơi mỗi ngày (thống kê trực tiếp trên website https://xvip.me/).
Cổng Game Đổi Thưởng Mới Nổi – Xvip
Xvip là cổng game đổi thưởng uy tín, thành lập năm 2023 và được chứng nhận hợp pháp bởi Isle of Man Gambling Supervision Commission. Với sự uy tín và tin cậy từ tổ chức giám sát này, cổng game cam kết mang đến môi trường chơi game công bằng và an toàn cho người chơi.
Với số vốn đầu tư lên đến hàng triệu đô đến từ CEO Trung Đỗ, cổng game này đã vươn mình trở thành một trong những cổng game mới nổi được ưa chuộng nhất hiện nay. Chỉ tính riêng trên website: https://noobe.io/, ứng dụng Xvip đã nhận được 300.000 lượt tải và hơn 1.000 lượt chơi mỗi ngày.

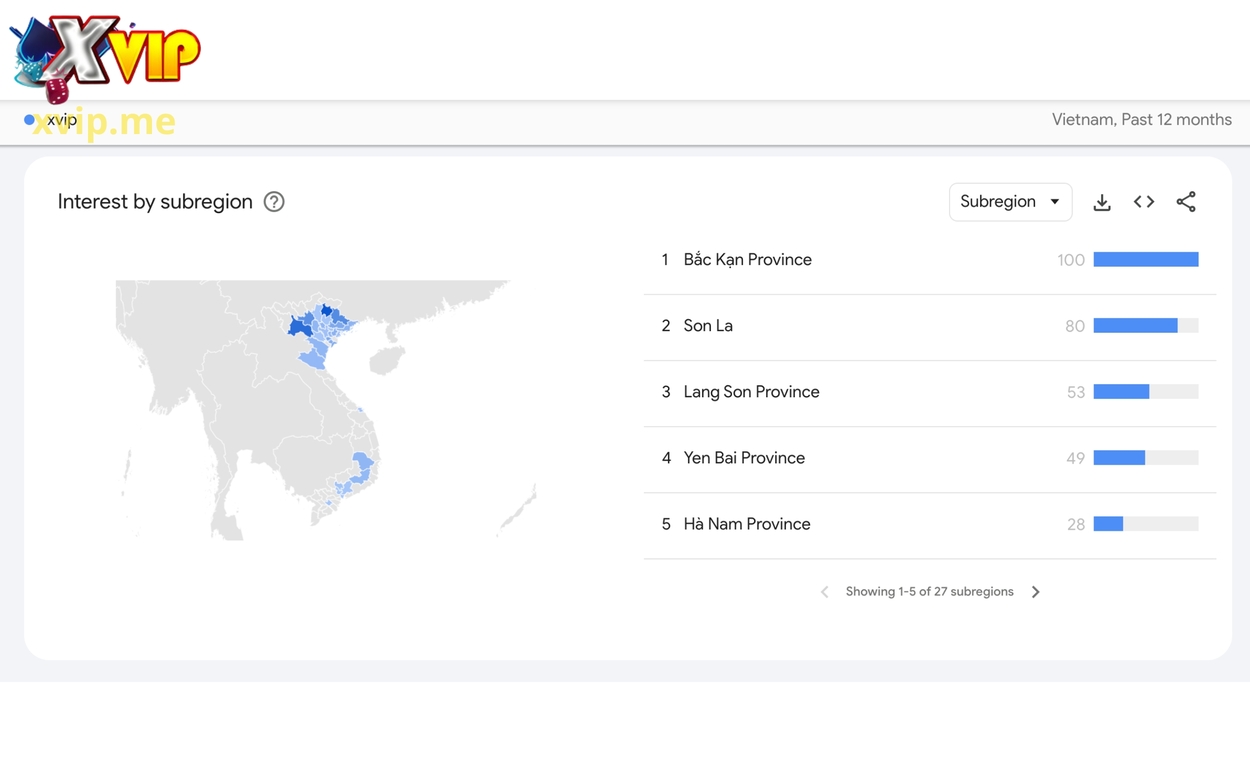
Xvip Nhận Vô Số Lượt Ưa Thích Khắp Việt Nam
Với những ưu điểm như: bảo mật tuyệt đối, giao dịch xanh chín, vô số khuyến mãi,… Xvip đã nhận được vô số lượt quan tâm từ cộng đồng game thủ tại Việt Nam. Điều này được minh chứng rõ ràng từ dữ liệu được thống kê tại Google Trend, cụ thể như sau:
- Bắc Kạn chiếm lượt ưa thích cao nhất với tỷ lệ 100%.
- Tại Sơn La có đến hơn 80% game thủ ưa chuộng Xvip.
- 53% tay chơi tại Lạng Sơn tin chọn cổng game này.
- Tỷ lệ game thủ tại Yên Bái truy cập Xvip là 49%.
- Xvip mở rộng thị phần tại Hà Nam với tỷ lệ tin chọn 28%.
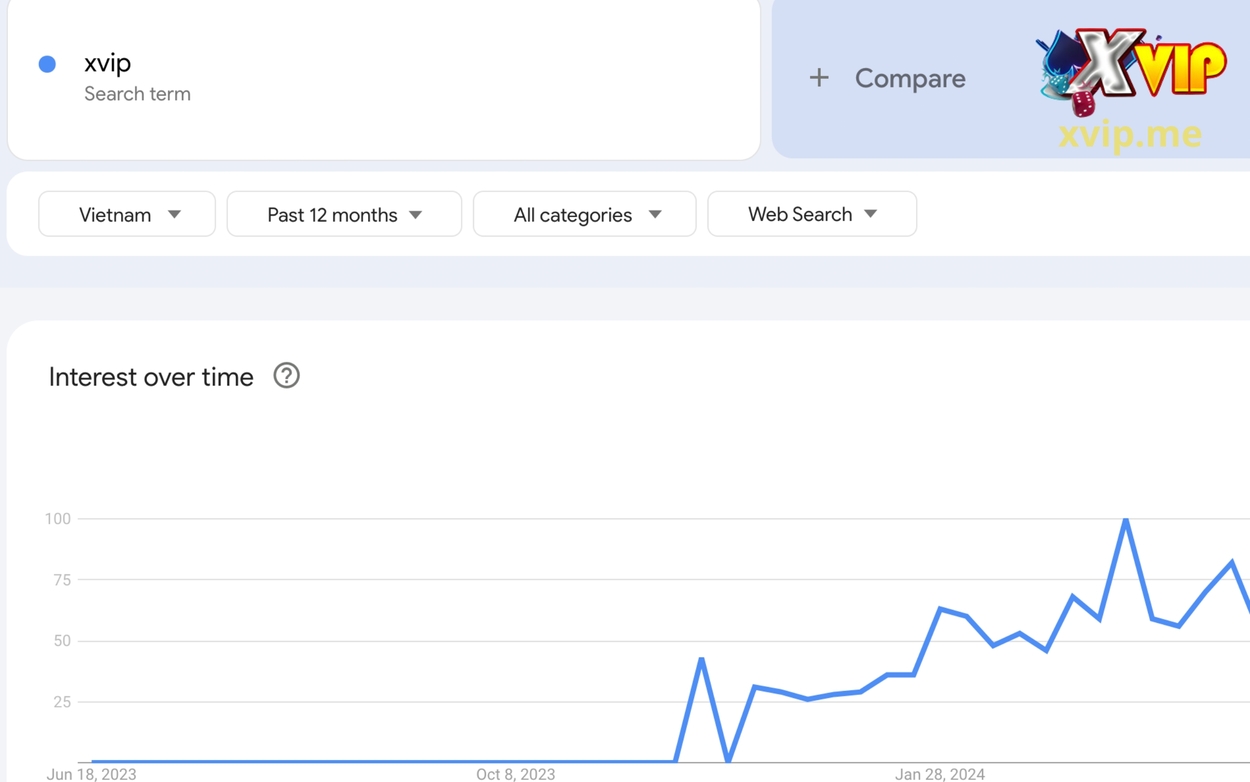
Lượt Tìm Kiếm Của Xvip Tại Thị Trường Việt Nam
Cũng từ dữ liệu tại Google Trend, con số tìm kiếm từ khoá “xvip” trở nên hot hơn bao giờ hết. Cụ thể từ ngày 8/10/2023 đến ngày 28/1/2024, tỷ lệ tìm kiếm cổng game này đã tăng vọt từ 0% lên đến 100% và có khả năng tăng trưởng hơn nữa trong tương lai.
Tổng Hợp Các Thể Loại Game Siêu Hot Tại Xvip
Để mang tới trải nghiệm hấp dẫn và trọn vẹn nhất dành cho người chơi. Kho game đỉnh cao tại cổng game chính là yếu tố quan trọng “giữ chân” người tham gia hiệu quả nhất. Dưới đây là tổng hợp kho game cá cược đỉnh cao chỉ có tại Xvip

Game Bài Đổi Thưởng Xanh Chín
Cổng game Xvip nổi bật với nhiều trò chơi bài đổi thưởng, mang lại trải nghiệm giải trí hấp dẫn và cơ hội nhận thưởng lớn cho người chơi. Dưới đây là một số trò chơi nổi bật:
- Xóc Đĩa: Trò chơi truyền thống với cách chơi đơn giản, người chơi dự đoán kết quả của 4 đồng xu sau khi được xóc. Tỷ lệ thắng cao, dễ chơi, và có thể tham gia nhiều bàn chơi cùng lúc.
- Sicbo: Là trò chơi xúc xắc thú vị, người chơi dự đoán tổng điểm của ba viên xúc xắc sau khi được lắc. Ưu điểm nổi bật của trò chơi là nhiều cách đặt cược với các mức thưởng khác nhau, mang lại sự hồi hộp và thú vị.
Game Nổ Hũ (Slots) Hấp Dẫn
Không thể bỏ qua những trò chơi nổ hũ hấp dẫn. Cổng game nổi bật với 2 trò chơi sở hữu tỷ lệ thắng cao được nhiều người chơi yêu thích:
- Kim Cương: Một thế giới lấp lánh của những viên kim cương quý giá. Với giao diện đẹp mắt và các vòng quay đầy kịch tính, trò chơi hứa hẹn sẽ mang đến những phần thưởng lớn và trải nghiệm thú vị.
- Đào Sập: Mang chủ đề khai thác mỏ vàng, nơi người chơi sẽ nhập vai vào những người thợ mỏ tìm kiếm kho báu. Các vòng quay trong trò chơi này đầy ắp những bất ngờ và cơ hội trúng giải thưởng lớn, tạo nên sự hấp dẫn khó cưỡng.

Game Casino Siêu Hiện Đại
Xvip tự hào mang đến cho người chơi những trải nghiệm casino trực tuyến siêu hiện đại và hấp dẫn nhất:
- Evolution: Nổi tiếng với các trò chơi casino trực tiếp chất lượng cao, bao gồm Blackjack, Roulette và Baccarat. Với công nghệ phát sóng tiên tiến, người chơi sẽ có cảm giác như đang tham gia vào các sòng bài thực sự.
- AE Sexy: Sảnh game nổi bật với các dealer hấp dẫn và chuyên nghiệp. Các trò chơi như baccarat, roulette và sicbo được trình diễn trong một không gian sống động và thu hút.
- WM Casino: Cung cấp một loạt các trò chơi cổ điển và mới lạ, từ baccarat đến dragon tiger. Với giao diện thân thiện và dễ sử dụng, WM Casino mang lại trải nghiệm chơi game mượt mà và thú vị.
- Betgame: Tập trung vào các trò chơi cá cược nhanh và hấp dẫn, phù hợp cho những ai yêu thích sự kịch tính và tốc độ. Các trò chơi phổ biến bao gồm poker, blackjack và nhiều game mini thú vị khác.
- BetSoft: Là nhà phát triển nổi tiếng với các trò chơi slot 3D ấn tượng, cùng với các trò chơi bàn và video poker chất lượng cao. Đồ họa đẹp mắt và âm thanh sống động chắc chắn sẽ làm hài lòng những người chơi khó tính nhất.

Mini Game Đổi Mới
Xvip không ngừng đổi mới và phát triển để mang đến cho người chơi những trải nghiệm thú vị và hấp dẫn.
- Tài Xỉu: Trò chơi dựa trên kết quả của ba viên xúc xắc. Người chơi đặt cược vào “Tài” (tổng điểm từ 11 đến 17) hoặc “Xỉu” (tổng điểm từ 4 đến 10).
- Tài Xỉu MD5: Phiên bản nâng cấp của Tài Xỉu với cơ chế bảo mật cao hơn, sử dụng mã hóa MD5 để đảm bảo tính minh bạch và công bằng trong kết quả.
- Bầu Cua: Trò chơi dân gian truyền thống, nơi người chơi dự đoán hình ảnh xuất hiện trên ba viên xúc xắc. Các hình ảnh bao gồm Bầu, Cua, Tôm, Cá, Nai và Gà. Trò chơi này mang đến cảm giác quen thuộc và vui nhộn cho người chơi.

Lưu Ý Khi Tham Gia Cổng Game Xvip
Khi tham gia cổng game, người chơi cần chú ý một số điểm quan trọng để đảm bảo quá trình nạp tiền diễn ra thuận lợi và an toàn:
- Cập nhật thông tin tài khoản ngân hàng: STK nạp tiền của Xvip được thay đổi liên tục. Trước khi thực hiện bất kỳ giao dịch nạp tiền nào, người chơi cần làm mới và kiểm tra STK hiển thị trên giao diện game.
- Không lưu trữ STK cũ: Người chơi không nên lưu STK để sử dụng cho các lần nạp tiền sau. Mỗi lần nạp tiền, hãy chắc chắn rằng bạn sử dụng STK mới nhất được hiển thị trên game.
- Kiểm tra thông tin kỹ lưỡng trước khi chuyển tiền: Đảm bảo rằng STK bạn sử dụng để nạp tiền là STK đang hiển thị trên game tại thời điểm thực hiện giao dịch. Chuyển tiền vào STK không còn hiển thị trên game có thể dẫn đến mất tiền.